Hardly a day goes by that we don’t hear of another data breach involving a prominent Australian brand. 
As cyber-attacks become more frequent and malicious, the onus is on organisations to maintain a strong level of awareness and take proactive steps to reduce the risk to their business and customers.
As a startup concerned with generating cash flow and gaining a foothold in the market, cyber security may be one of the last things on your mind. However, and particularly with the current cyber threat landscape, being haphazard about your business’s cyber approach could cost you dearly.
Perhaps now more than ever before, customers are taking an active interest in how their personal information is managed. They want to feel confident that the service provider is keeping their personal information safe and secure, yet building this trust is not easy. Millions have been affected by data breaches compromising their privacy, with every new breach chipping away at their confidence in digital security.
For businesses that understand the importance of digital trust and choose to place cyber security at the heart of their operations, this represents an opportunity to gain a very real competitive advantage.
Cyber security as a strategic tool
The World Economic Forum recently posted an article stating:
“…for organizations to be truly successful, the perception of cybersecurity must shift from being a ‘check box’ activity to being a strategic tool that can further drive business objectives and build customer trust.”
As a startup, it’s important to remember that you can only promote trust in your digital systems if you trust in them yourself.
This can be a great starting point, as it will help you determine what you know (and don’t know) about your digital systems so you can start building a cyber security action plan.
Try not to rush out and spend money you don’t have on complex enterprise solutions.
A targeted approach is usually much more effective, as it recognises the unique risks that apply to your business and takes firm steps to reduce or eliminate them.
There is no ‘one size fits all’ solution when it comes to cyber security, and today’s “pay-for-use” subscription services are a recognition of this. They offer a relatively simple and cost-effective way to address specific cyber risks, with the ability to scale up or down based on your business needs.
It can be difficult to determine the exact services you need, which is why it’s often valuable to engage a cyber security expert to conduct a review for you. They can:
- Benchmark your environment against best practice
- Identify gaps
- Recommend solutions and strategies
- Advise on internal processes and policies
Especially for a start-up, getting your processes and policies correct early on can save you a lot of hassle down the track. They also set a standard for cyber awareness in the business by declaring, 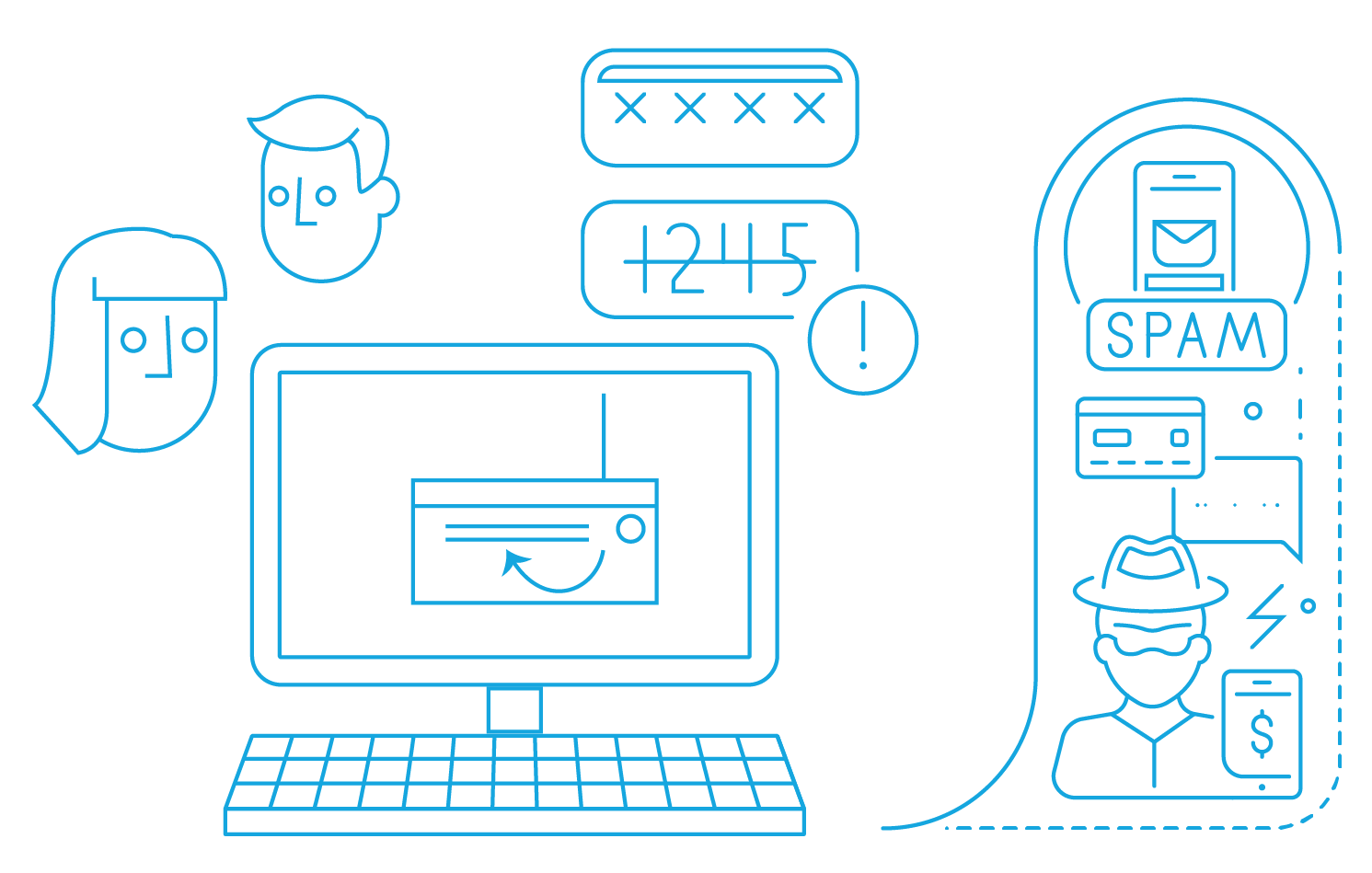 “We care about cyber security, and this is how we do things here.”
“We care about cyber security, and this is how we do things here.”
Your policies could include fundamental cyber hygiene practices, such as enforcing password policies or requiring staff to acknowledge a set of acceptable use policies relating to systems and device usage.
They should also include privacy-related policies, such as privileged access management, where access to personal information is only granted on a need-to-have basis.
Essential data privacy considerations also include how personal data is being classified and transmitted to prevent unauthorised access or minimise the risk of any data exposure and breaches.
Being a startup, it is common for IT and cybersecurity functions to be outsourced. In this case, vendor management plays a critical role in creating and brokering digital trust.
Selection criteria should include proper vetting procedures, such as requesting cyber security related assurance reports and certifications for industry-accepted benchmarks - ISO27000, Essential 8, NIST Cyber security framework, for example.
It’s important to remember that outsourcing cyber security functions does not obliviate your obligations as a data owner.
To build a comfortable level of trust in your customers, communicate your data protection strategies and initiatives with them. You can do this at all stages of the customer journey – from the first time you ask for their email, to when you process any transaction, to how you display your privacy policy on your website.
What to do if you experience a breach
At the end of the day, you may do everything perfectly and still fall prey to an attack.
If this happens, try not to stick your head in the sand and hope it will blow over. Instead, act quickly and communicate clearly with everyone who has been affected by the breach. Be transparent about what happened, identify the gaps present resulting in the incident and let your customers know what you are going to do about it.
Keep your customers up to date with the latest developments and be sincere in apologising for what has happened. Put yourself in their shoes and ask how you would want a company to react.
By adopting this mindset, you may reduce the reputational impacts of the breach – allowing you to maintain positive relationships with customers and learn from your mistakes so you can do better next time. Focus not only on the things you need to do but also on the things that you could and should be doing when it comes to protecting customer information.
For more information
Please contact Ashwin Pal or visit our webpage for more information on our Cyber-Security & Resilience services.